So I’ve been waiting for this insane sort of a situation to happen for about 20 years now. That is, a major part / piece of international IT infrastructure failing. I’m of course talking about the recent crowdstrike failure.
So I’ve been waiting for this insane sort of a situation to happen for about 20 years now. That is, a major part / piece of international IT infrastructure failing. I’m of course talking about the recent crowdstrike failure.
With regards Cyber Security, large companies like to pay someone else to take care of the problem for them. It means they can avoid accountability and pass the buck to someone else. Strange how the crowdstrike stock price is tanking!
https://www.google.com/search?q=crowdstrike+stock+price
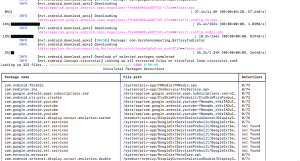
The crowdstrike issue was / is an example of humans loving the fact that they can pass the buck. It’s also about environments that lack diversity and this creates or leaves open a single point of failure. Many many machines are going to have to be physically restarted and modified to sort this problem, and the answer to all this is something IT tends to shy away from – that being an environment of variation can be a lot more robust.
What do I mean by this? The answer is a variety of operating systems (ie Mac, Linux, Bsd even Android or ChromeOS) both at the server and user level. Not to mention a variety of routers and switches all carefully constructed to operate together. It’s an interesting thought experiment that few people want to consider because, we are all about the bottom dollar! We want things to be as easy as possible!
The crowdstrike insanity is a huge home goal event, an embarrassing hiccup for a number of companies and even your humble author (I had to go and find cash to try to pay for my weekend vino! By the time I came back the store had closed, because even their cash draws no longer could function)!
It will be interesting to see if we learn anything from this large hiccup that took out about 8.5 million machines. Many of which were parts of important infrastructure including including airlines, banks and hospitals.
A few interesting observations. George Kurtz, the CEO of Crowdstrike has gone thru something similar before – In 2010 while he was working for McAffe a similar problem, that caused a global IT meltdown due to a faulty update. CTO at this time was George Kurtz! Who would have thought!
In a number of companies I have worked for we had a rule. Never, ever run out a major update on a Friday! Unless the client is willing to pay for out of hours weekend support. Guess George is still working on that lesson.
Now I want you to put your thinking caps on and go read about what notpetya did. Think about what you might do if we ever have total Cyber warfare!