Ransomware, the stuff of your worst nightmares. It seems as if this is getting very serious. The Darkside is a group of hackers that have recently caused a lot of pain. For example in the US the Colonial Pipeline has been shut down – that’s 5,550 miles of pipe for the oil industry. Meanwhile in Washington DC police are also subject to ransomware – they have allegedly offered $100,000 dollars – apparently this was not enough! So not only are they locking up all those machines they are also sifting thru all your data, and exposing that infomation on the net, using it as an extra point of leverage.
Ransomware, the stuff of your worst nightmares. It seems as if this is getting very serious. The Darkside is a group of hackers that have recently caused a lot of pain. For example in the US the Colonial Pipeline has been shut down – that’s 5,550 miles of pipe for the oil industry. Meanwhile in Washington DC police are also subject to ransomware – they have allegedly offered $100,000 dollars – apparently this was not enough! So not only are they locking up all those machines they are also sifting thru all your data, and exposing that infomation on the net, using it as an extra point of leverage.
As noted in the Kerbs article. “Security firm Emsisoft found that almost 2,400 U.S.-based governments, healthcare facilities and schools were victims of ransomware in 2020”.
How do you defend against this? So there is a few ways to approach this – one is to air-gap and remove mission critical computers from the internet. Think about it, that payroll machine? That set of servers that run the production plant? Do they really need to be on the internet 24 /7 ? May be you have one cable that you physically connect when and only when you need to (to run OS software and security updates). Maybe you set up a seperate airgaped network for that server and the network of production machines. Silo those machines.
Anti virus software. Use it but configure it so it doesn’t stop your functionality. This can sometimes feel like a black art, and it’s often hard to get the balance right but it is a good idea for a lot of users.
Backup your files. You have that latest pitch? Is it backed up? Can you restore it? Do you know how long it would take to re build your server? Those 20 machines that are the core of your company? Knowing this and the cost of the emergency rebuild process is something that you should be on to.
Get rid of those very old machines! If you have an old machine that’s never been updated it’s a huge risk vector. Spend some time and money now before it costs you big time.
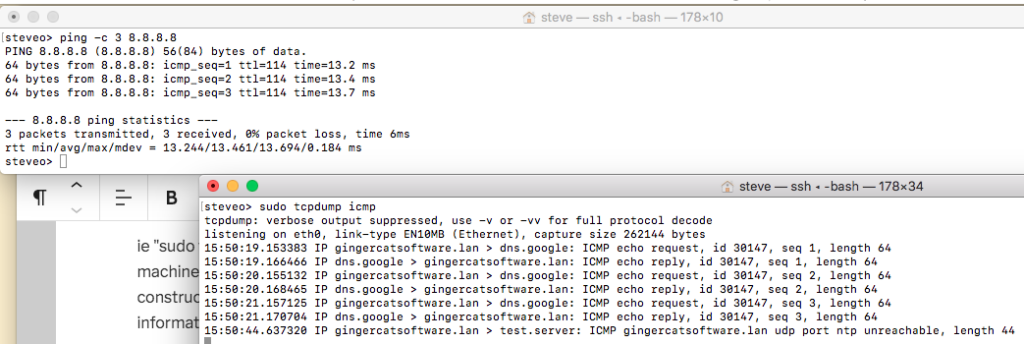
Use your firewall /s! This is a great starting point, if your activley monitoring things use that info – put it back into your firewall. Do you have a mcahine build you maintain? Why not use that firewall info in your machine builds?
What ever you do “Have a plan!” A cyber security plan.
Being able to protect and if necessary re build you network from scratch is one way of beating these crooks – but if you start looking into the detail of what’s involved it’s scary stuff. Stay safe on the interwebs people!
Related reading – Darkside hack
https://krebsonsecurity.com/2021/05/a-closer-look-at-the-darkside-ransomware-gang/
https://en.wikipedia.org/wiki/Colonial_Pipeline_cyberattack
https://www.intel471.com/blog/darkside-ransomware-colonial-pipeline-attack
Washington DC Police
https://www.vice.com/en/article/5dbgbk/washington-dc-police-allegedly-offered-dollar100000-to-hackers-to-stop-leak